Pipeline is getting triggered on branch which are not mentioned under “only”
I have a CI config file (like mentioned below), in that file I have only mentioned to run the pipeline on specific branch i.e., main, development and test. It is working as expected for all the users who has access to the repo with developer role; but only for specific user if they are pushing their code on any branch a failed pipeline is being generated. This uses also has the same developer role as others
- I am using GitLab.com and the version is as below*
- GitLab: 14.4.0-pre
- Runner: 14.3.0-rc1
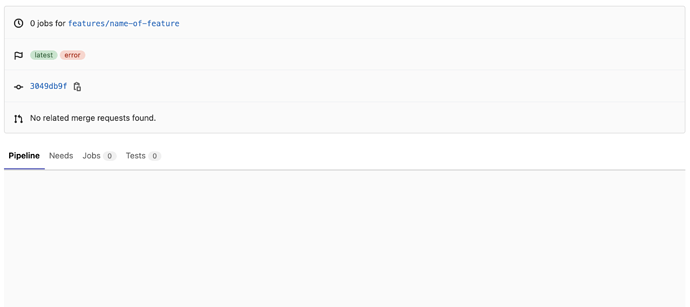
Here are few screenshot for the same
.gitlab-ci.yml
stages:
- buildimg
- gkedeploy
variables:
_GCR_HOSTNAME: us.gcr.io
_IMAGE_TAG: $_GCR_HOSTNAME/$PROJECT_ID/$CI_PROJECT_PATH:$CI_COMMIT_REF_SLUG
_K8S_NAMESPACE: my-app
Build Docker Image:
image: docker:stable
stage: buildimg
when: manual
environment: $CI_COMMIT_REF_NAME
only:
- development
- test
- main
services:
- docker:dind
before_script:
- docker --version
- echo $_IMAGE_TAG
- echo $GCR_MANAGER_KEY | docker login -u _json_key --password-stdin https://$_GCR_HOSTNAME
script:
# Build and tag image for GCR
- docker build -t $_IMAGE_TAG .
# Push image to GCR
- docker push $_IMAGE_TAG
after_script:
- docker logout
.prepare_step: &prepare_step
- echo $_IMAGE_TAG
# Replacing the Namespace token with correct value
- sed -i "s#__K8S_NAMESPACE__#$_K8S_NAMESPACE#" ./k8s/namespace.yml
Deploy in Google Kubernetes Engine:
image: google/cloud-sdk
stage: gkedeploy
when: manual
environment: $CI_COMMIT_REF_NAME
only:
- development
- test
- main
before_script:
- *prepare_step
script:
- echo $SERVICE_ACCOUNT > /tmp/$CI_PIPELINE_ID.json
- gcloud auth activate-service-account --key-file /tmp/$CI_PIPELINE_ID.json
- gcloud config set project $PROJECT_ID
- gcloud config set compute/zone $COMPUTE_ZONE
- gcloud container clusters get-credentials $GKE_CLUSTER
- kubectl apply -f ./k8s/namespace.yml
after_script:
- rm /tmp/$CI_PIPELINE_ID.json
It will be helpful for me if someone point out how to prevent it.